-
Wireless network connection: Basics and beyond
When people mention wireless network connection, they’re usually talking about Wi-Fi. The terms are often used interchangeably, but Wi-Fi is actually just one type of wireless technology. “Wireles...
-
How to delete a Tinder account (step-by-step)
Tinder is a convenient app for meeting new people, but not everyone sticks around long-term. Whether you’ve found a match, want to reduce your digital footprint, or simply no longer use the service,...
-
How to set up a virtual machine safely and avoid common mistakes
Virtual machines (VMs) let one physical computer run multiple OSs. Setup requirements vary depending on the hypervisor and the isolation/networking choices, so it can feel complex. This guide explains...
-
What is cyber insurance and how does it work?
Cyber insurance is a type of coverage designed to protect businesses and individuals from the financial losses usually caused by cyber incidents. As data breaches, ransomware attacks, and online fraud...
-
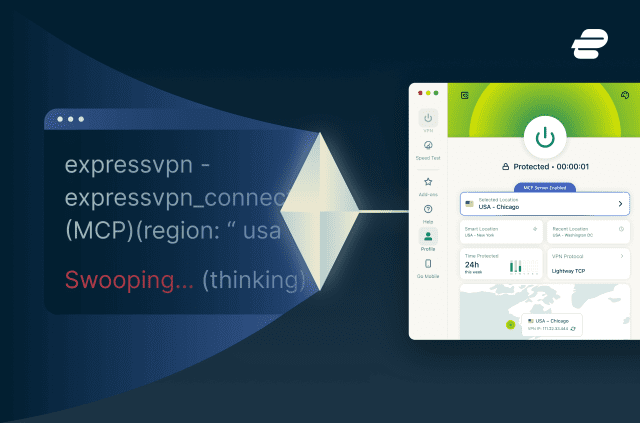
The AI era requires a new way to control your VPN. So we built it.
ExpressVPN is the first VPN provider to adopt the Model Context Protocol (MCP). We built a strictly local bridge that lets your AI coding assistants manage your network routing without ever opening a ...
-
How to perform a factory reset on your Oculus Quest
Common Oculus Quest issues, like buggy apps, slow performance, connectivity issues, or freezes, are often easy to fix. However, if these issues persist, a factory reset may help. This guide explains h...
-
What is HTTP/3 and should you use it?
HTTP/3 is the newest version of Hypertext Transfer Protocol (HTTP), the protocol that allows browsers to request web pages and servers to send them back. It defines how those requests and responses ar...
-
How to delete your Tumblr account: Fast desktop and app walkthrough
Whether you're stepping back from social media, tidying up your digital footprint, or simply finished with the platform, deleting your Tumblr account takes just a few minutes. This quick guide shows t...
-
Most secure Linux distro: Best picks by threat model
Choosing the most secure Linux distro is about matching the system to its intended use, the sensitivity of the data it handles, and the level of setup and ongoing maintenance that are realistic. In ma...
-
How to make your X account private: A comprehensive guide
X (formerly Twitter) lets you control who can see and interact with your posts. It adds a layer of privacy and security while still allowing you to post, read, share, and comment as usual. People can ...
Featured